The aftermath of Spectre and Meltdown security vulnerabilities is still ongoing, and various new attacks (varying in severity and legitimacy) have surfaced online since Google’s Project Zero bought them to the fore. However, there really is a new subclass of speculative-execution attack, yet again outlined by Google and Microsoft.
Don’t be alarmed, as with the last Spectre and Meltdown vulnerabilities, this new attack is realistically about as dangerous to your home PC as a cat napping on your exhaust fans. That’s not to say it has no potential to be dangerous in the wrong hands, but no exploits have been spotted in the wild as of yet, and the current mitigations for Spectre Variant 1 will also make Variant 4 exploits pretty tricky.
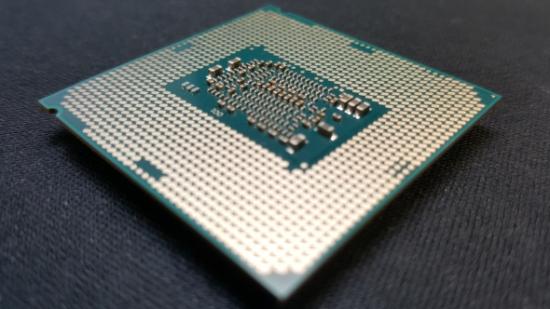
Get more processing power for your money with the best AMD and Intel CPUs around.
Variant 4, or Speculative Store Bypass (SSB), utilises the same speculative execution channels as other variants outlined previously, and this means it opens up data extrapolation from a side channel – this time, that means a language-based runtime environment, the likes of which are most commonly found in web browsers.
As most common processor architectures feature similar construction and utilise speculative execution in some way during function, Variant 4 could apply in some way to many processors and architectures from various manufacturers, including Intel, AMD, and ARM.

Intel are now working on full Variant 4 mitigation steps, which will come in the form of microcode and software updates, and they’ve already started rolling out beta updates to OEMs. AMD, on the other hand, released a statement confirming incoming Windows and Linux OS mitigations within software updates that will roll out in the usual way across these platforms. These will apply all the way back to AMD’s Bulldozer platform products.
Variants 1 – 3 were all discovered back in January, unleashed on the world by Google’s Project Zero team. Since then, various microcode and OS updates have rendered them largely obsolete, although the fallout has led to various new vulnerabilities making it to the light of day, including Spectre Variant 3a and some debatable security ‘flaws’ outlined by CTS Labs.
Intel and AMD are both promising to fix Spectre issues within upcoming hardware generations – you can expect these fixes in silicon within Intel Coffee Lake processors later in the year, and AMD Zen 2 chips in 2019.
What does all that mean to you? Keep your PC up-to-date and don’t make yourself a target to nefarious actions is, and always will be, the best course of action to avoid these situations. While often forgotten beyond first installation, keeping your motherboard’s BIOS updated is a critical step in keeping your PC secure and performing at its best – so make sure to check your board manufacturer’s website for the latest version available.