Security researchers have uncovered a new system vulnerability within Intel CPUs. Zombieload, as the flaw is unfortunately called, could allow a nefarious hacker person to gain access to sensitive and otherwise private data in what is described as a “Meltdown-type effect.”
The Zombieload flaw, officially known as “Microarchitectural Data Sampling,” or MDS, allows a program to read data that’s being processed by another program that it would not otherwise be permitted or able to gain access to. According to Intel, Zombieload is difficult to exploit and does not explicitly allow a user to leak specific data, rather this is dependent on the other programs running on the exploited machine.
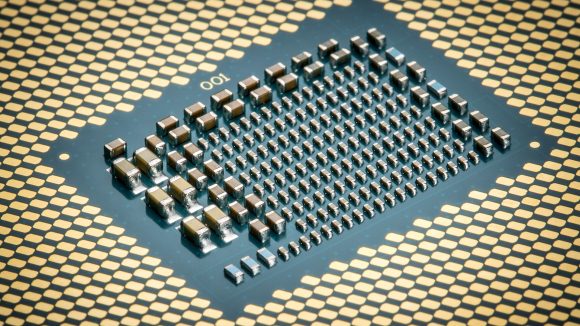
Zombieload attacks are reportedly only possible on Intel CPUs produced during or after 2011, but even if that includes your CPU there’s no need to panic. Most major OS providers have already rolled out patches coinciding with Intel microcode to fix the flaw. The mitigations alone have only a minor impact on performance, but, depending on a user’s workload and security requirements, there’s an argument to be made for disabling SMT, or HyperThreading, entirely.
“We conclude that disabling hyperthreading, in addition to flushing several microarchitectural states during context switches, is the only possible workaround to prevent this extremely powerful attack,” a research paper describing the Zombieload flaw, authored by researchers at Graz University of Technology, Cyberus Technology, Worcester Polytechnic Institute, and KU Leuven, says.
Time for a change? These are the best CPUs for gaming
HyperThreading is a proprietary Intel technology, built upon simultaneous multithreading (SMT), that allows a CPU’s thread count to double from a 1:1 thread-to-core ratio to 2:1. A six-core processor with HyperThreading enabled will feature 12 threads, making it far better suited to multithreaded workloads.
HyperThreading has been the signature feature for the more pricey i7s and i9s for years, often being one of the few differentiating factors between the high-end chips and the midrange i5 processors. Without HyperThreading enabled, i7 processors feature just marginally higher clock speeds and cache sizes than their cheaper i5 alternatives.
Intel does not recommend disabling HyperThreading in every case, instead recommending customers should “consider how they utilize SMT for their particular workloads, guidance from their OS and VMM software providers, and the security threat model for their particular environment.”
How will Zombieload affect my computer’s performance?
Intel’s benchmarks suggest only a marginal decrease in within some tasks while Zombieload mitigations are in place.
Within the company’s in-house testing, a Core i9 9900K with HyperThreading enabled drops 3% performance in WebXPRT 3 testing. At best, it gained 1% within SPECint_rate_base 2017 (1 copy) testing.
However, with HyperThreading disabled, that same chip suffered a 9% drop in SPECint_rate_base 2017 (n copy) testing, and 7% in SYSmark 2014 SE.
Datacentre workloads come off worse, however. While the mitigations have little to no affect on general compute tasks with both the Intel Xeon 8180 and E5 2699 v4 and HyperThreading enabled, storage tasks were up to 14% slower.
And with HyperThreading disabled, the Intel 8180 dropped 11% in general compute, and 19% in server side Java tasks.
Disabling HyperThreading is evidently the most damaging to performance, although not a measure that everyone will deem necessary or worthwhile. While no system can ever be entirely safe and secure, there have been no reports of Zombieload attacks out in the wild, and the chance of this particular attack affecting your system is awfully low. MDS has been deemed low to medium severity by CVSS standards.
AMD and ARM CPUs are unaffected by Zombieload, MDS-class vulnverabilities despite also utilising a simultaneous multithreading within their processors.
Various researchers have independently stumble across MDS-class vulnerabilities, including those stated in the aforementioned paper – Intel, Microsoft, BitDefender, VUSec, CISPA, the University of Adelaide, Data61, and the University of Michigan. All were beholden to the same disclosure period.
Both the RIDL and Fallout speculative execution attacks are under the MDS-class umbrella, so you may see these terms also being used to describe a specific form of attack.
According to a report by nrc.nl, the lion’s share of the RIDL attack discovery was carried out by a team of researchers at the VU University Amsterdam, after somewhat accidentally stumbling across the severe bug. The university was the only one to receive a monetary reward from Intel’s Bug Bounty Program of $100,000, or the maximum reward available.
But, according to the researchers, Intel originally attempted to downplay the severity of the leak, and failed to notify Google and Mozilla. The VU would eventually convince Intel to disclose the flaw in May after threatening to publish its own paper.
“If it were up to Intel, they would have wanted to wait another six months,” Herbert Bos, professor of system and network security at the VU, says.
how do i protect my pc from Zombieload attacks?
As always keeping your PC up-to-date with the latest patches is crucial to staying secure.
Since most gaming rigs run Windows, these updates are most crucial to gamers’ security. Microsoft recommends running Windows Update to install the latest security updates and Intel-sanctioned microcode updates. These may only be available from a specific OEM, so check around if need be.
Microsoft also recommends that “to be fully protected, customers may also need to disable Hyper-Threading.” But that’s up to your discretion.
Apple has also released a fix for all Macs and MacBooks released since 2011 running macOS Mojave 10.14.5, Sierra, or High Sierra, citing no performance degradation for most users. However, those of you that require full mitigation could suffer up to a 40% performance loss.
Mozilla and Chrome have also all rolled out security updates to their latest or upcoming releases, and Chrome OS has, by default, disabled HyperThreading.
Amazon AWS has reportedly been patched up against the attacks. Server-side workloads are most likely to be at risk and affected by potential exploitative attacks, which could yet again push AMD, which is unaffected by the latest vulnerability, to gain market share from its dominant rivals with EPYC.