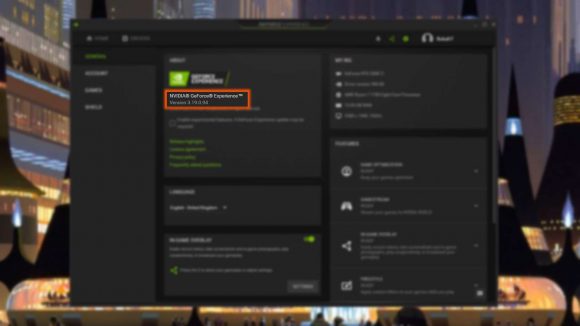
A security exploit was discovered in Nvidia’s GeForce Experience application in April and you need to make sure that, if you’re running the software, it’s updated to version 3.19 as soon as possible. Otherwise the haxxorz will get you. Or might get you. Admittedly, like a lot of the recent PC security panics, you’re unlikely to suffer at the binary hands of this code injection exploit, but it’s still always worth closing off an issue before it becomes one.
Nvidia was informed of the existence of the exploit on April 16, with the company confirming the security hole was going to be patched out by a GeForce Experience update to version 3.19 at the end of that month. The update went live on May 27 and Nvidia has since published the security update stating that the issue has been eliminated.
Though Rhino Security Labs, the company which first reported the exploit, is still recommending that if you don’t actually need to use GFE then “it is a good idea to simply uninstall it from your system to reduce the additional attack surface it introduces.”
Nvidia’s security bulletin claiming to address issues “that may lead to information disclosure, escalation of privileges, denial of service, or code execution” and explains that users will need to go and download the latest version of GFE, which you can find here.
I hear you: These are the best gaming headsets around today
The issue reported by Rhino Security Labs affects all versions of the software prior to the latest update and is described as: “a vulnerability in the Web Helper component, in which an attacker with local system access can craft input that may not be properly validated. Such an attack may lead to code execution, denial of service, or information disclosure.”
The security experts explain that the attack can be carried out via a browser, where a nefarious actor could convince a user to visit a certain website and just make a couple of clicks to open the exploit.
“Although this does require some user interaction,” says Rhino Security Labs, “it is minimal enough that tricking a user into performing the actions which are required to achieve this would be trivial.”
A second vulnerability is also referenced by the bulletin, where it incorrectly loads Windows system DLL files without validating the paths or signatures, leaving it open to an escalation of privileges, though the attacker will need local access to your machine.
Rhino Security Labs, however, does state that while the discovered command injection issue has been fixed in the latest version of GFE, there are still some some parts of the issue that Nvidia hasn’t patched out of the software which means the GeForce Experience API is still open to outside interaction via a browser.
So yeah, that’s going to add a little extra fuel to the ‘I’m not installing GFE’ fire.
Join in the conversation and comment on this article’s Facebook or Twitter posts.